Agentic bots and scripts have changed what an attack looks like. An orchestrated attack, sometimes running thousands of lookups across many email addresses in a short window can burn through API lookups before you have a chance to notice.
Temp Mail Detector now detects and gates these attacks automatically.
How It Stops Fake Users
Our API monitors the rate of incoming requests per root domain. When that rate crosses a threshold that indicates non-human or automated behaviour, the root domain is gated: further lookups against addresses at that domain are blocked at the infrastructure level before they consume lookups.
A single attacking domain does not spawn unlimited sub-variants that bypass the gate. The gating operates at the domain root, which means the full surface of an attack is covered by a single action.
Why This Matters
Without rate-based gating, a sustained attack has a direct financial consequence. Every lookup costs credits, regardless of whether it was triggered by a real user or an automated attacker cycling through addresses. If an attacker targets your integration, you pay for it.
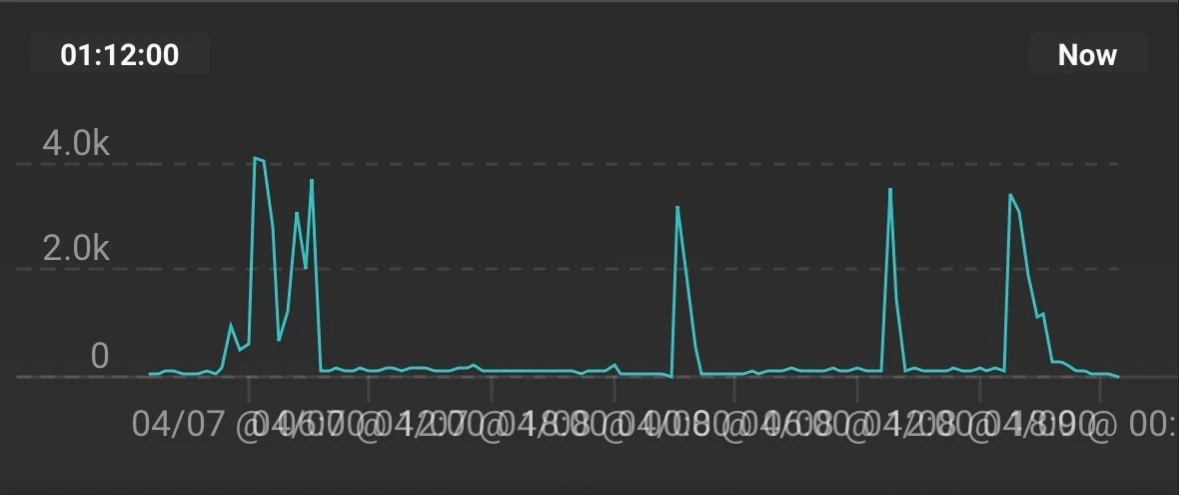
The above image shows part of a multi-day campaign against one of our customers. This was prior to our gating feature being introduced.
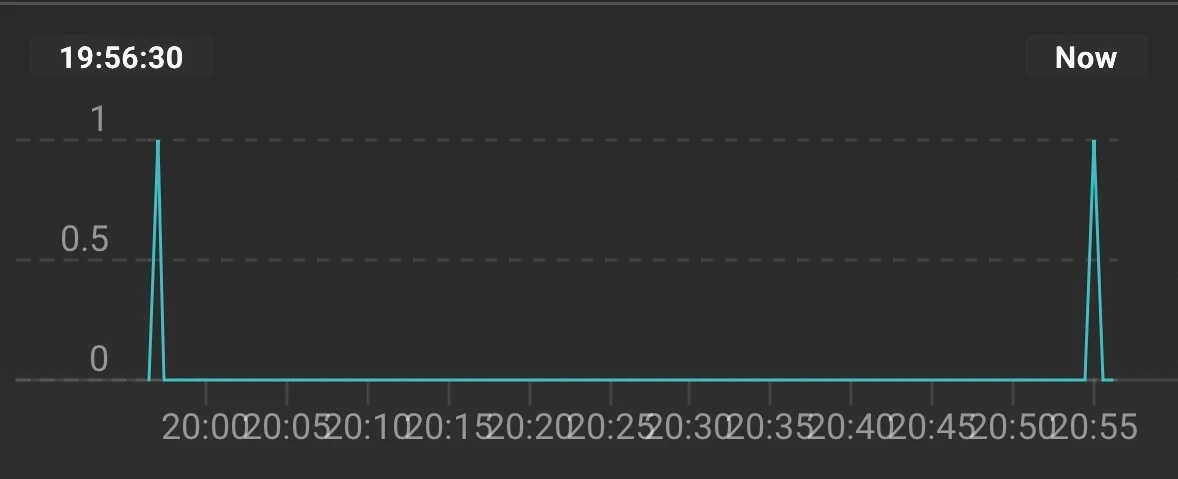
With the new gating feature, requests will still come in, but once enable, thousands of fake accounts are subsequently rejected.
For customers under attack, the gate feature changes everything. Once an attack pattern is detected, lookups from that domain stop counting against your balance. You are not penalised for traffic you did not generate and did not want.
Stopping Agentic Bots
Standard rate limiting catches simple scripts. Agentic bots are different. They are built on AI orchestration layers, spread requests across time intervals, IPs, geographies and vary their patterns to evade naive detection. The attack surface they create is not always a spike on a chart but rather a sustained, distributed flow that looks almost normal in isolation.
The rate analysis built into this feature is designed with that threat model in mind. It looks at behavioural patterns across the request window, the underlying infrastructure of the domains provided, then takes action to protect your service.

What You Need to Do
Quite simply: nothing. The protection is active by default on all accounts. No configuration is required.
If a domain is gated due to attack detection, it is released automatically once the anomalous pattern subsides. There is no manual review step and no support ticket required on your end. Gates are applied per customer and per domain, so noisy neighbours won’t affect your signup flow. Further, your existing implementation will see the domain risk score shoot up and the block flag flip to true, meaning your application will automatically reject those signups.
